Stable operation of the Windows operating system is achieved due to the functioning of many processes, some of which are simply hidden from the users' eyes. This “stealth” is characterized by the fact that the computer operator has no reason to interfere with the work of these system processes, which explains the reluctance of users to pay attention to the activity indicators in the “Task Manager”. But this happens only for the time being until the normal work of Windows is disrupted, and then, in search of sources of excessive load, each user accesses the information in the Task Manager and sees that some processes have a particular impact on the speed of the computer. And about one of these "troublemakers" and will be discussed in this article.

Features of the Winlogon.exe process.
What is it
So, the process “Winlogon.exe” or “Windows Logon Application” is a system component that has an extensive functional set for working with a user account. The structure of this component and all its powers have a rather complicated structure, to understand the wilds of which simply does not make sense. To understand its importance, you can simplify the list of his cases as much as possible and select the following items from them:
- Responsible for the safety of the desktop. Roughly speaking, every time a user sees a message about the need to enter a password to log into his account, this is precisely the evidence of the success of the “Winlogon”.
- Monitoring the integrity and security of user data, "collaborating" with the standard "SAS".
- Monitoring the activity of network connections.
- Validation of the use of the operating system version.
- Ensuring proper functioning of screensavers (with active modes of operation).
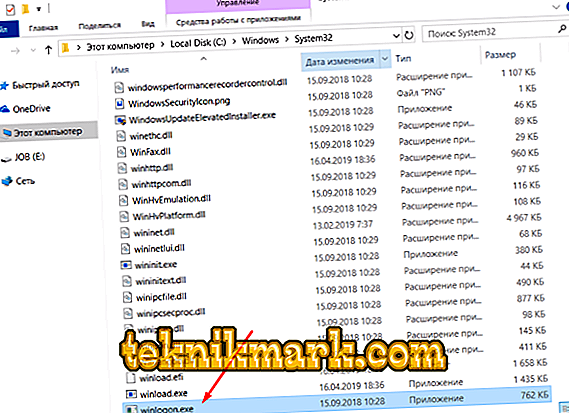
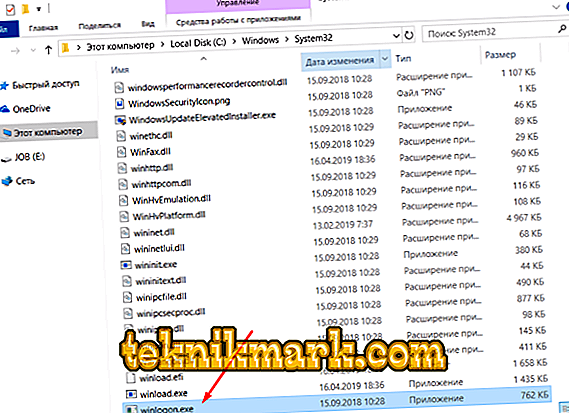
Given the importance of this functionality, it should be noted, and also taking into account that the executable file of the process under consideration is located in the system directory - C: \ Windows \ System32, its unauthorized deactivation may lead to short-term or long-term disruptions in the operation of the operating system. Therefore, if you have witnessed that in “Task Manager” in “Winlogon.exe” or in “Windows Logon Program” (this may be its name), the indicators of the created load are highlighted in red, in no case can you complete it yourself work until the reasons for this are clarified.

Why load is created
The answer is simple. In the work of “Winlogon” just can not create such a load, which would most directly affect the quality of the operating system. If there is such a load, then its culprit should be sought in the possible infection of the computer with virus software. It will not be a secret for anybody that various viruses like to pretend to be system components, since “such a shell” creates a good guarantor of their immunity. This statement is directly related to the component considered in this article. Hiding a virus under the guise of "Winlogon" can very appropriately and without careful study to identify the "substitution" is extremely problematic. Base your suspicions on the following points:
- During normal operation of the computer in the “Task Manager” there is not and cannot be two variations of “Winlogon.exe”. If you observe two representatives, then one of them is guaranteed to be a “spy”.
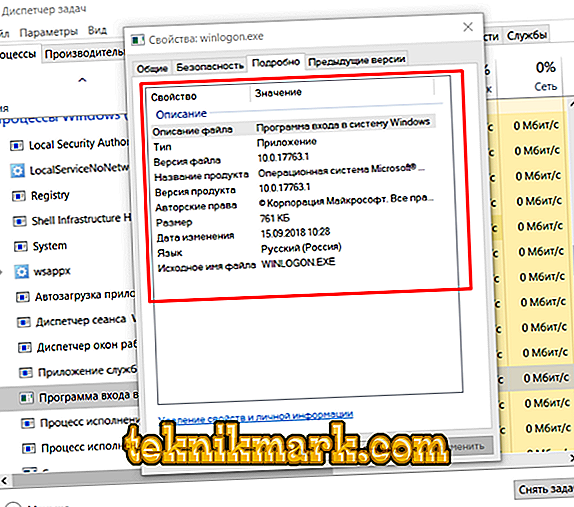
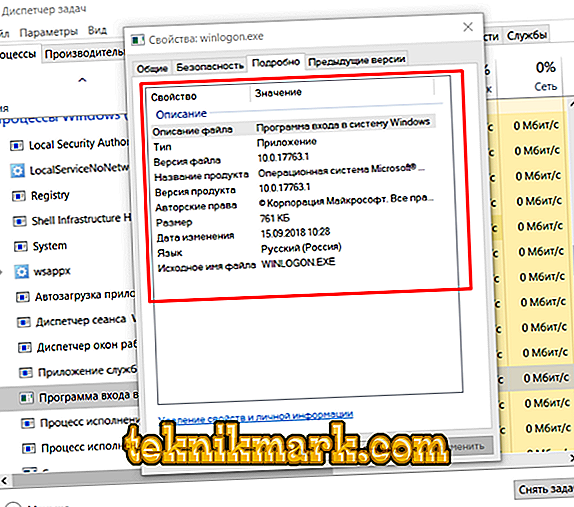
- Right-click on any of the "suspects" and select its "Properties", then go to the "Details" tab. Particular attention should be paid to the specified author, version and update date. It is mandatory that Microsoft should be listed here.
- Right-click again and select "Open File Location" to make sure that the executable file is "Winlogon.exe".
This information is sufficient to ensure that there are gaps in the security of your copy of Windows.
Conclusion
After identifying the offender, it is necessary to neutralize it with specialized antivirus software. It is advisable to use third-party utilities that differ from the antivirus presented on your computer, since this defender did not cope with his work and overlooked the “villain”. Utilities such as Dr.Web CureIt!, AdwCleaner and Malwarebytes can be mentioned as tips. The last thing that will be necessary to make sure is how well the installed antivirus works, perhaps it needs updating or more permissions to function.