Virtual networks based on VPN technologies are used for various purposes and today provide not only the construction of corporate networks or protection when using public connections, but also access to the Internet. In addition, thanks to VPN, visits to web resources are available bypassing locks while preserving privacy, which has most recently worried users. The process of setting up a VPN for each system has its own characteristics and can be performed in various variations. Depending on many factors, including the target destination and the type of network construction, there are several ways to implement the technology. We will look at how to configure VPN on Linux, and also clarify why this connection is applicable.

The method of setting up a VPN connection in Linux.
What is VPN and why is it needed?
First, let's look at what a Virtual Private Network is and how this type of technology is applicable. With VPN, you can connect any number of devices into a private network, and provide a secure channel for data transfer. So, using this type of connection, users can maintain privacy on the Internet and not worry about data integrity, including when working on shared networks. Connecting to a VPN prevents intruders from intercepting information, because the packet exchange route is securely protected by encryption and user authentication. The data is encrypted on the sender's side and follows the communication channel in an encrypted form, and is decrypted already on the recipient's device, with both of them implying a shared access key. With the use of VPN it is possible to create a reliable network on top of an unreliable (usually the Internet). User connection is not performed directly, but through a server connected to an internal or external network. This ensures privacy on the Internet, because in this case, the web resources will see the IP of the server to which the client is connected. The server will require an authentication procedure, as well as authentication, and after the user is authorized, work with the network is possible. VPNs are most commonly used in the following cases:
- Connecting to the Internet via VPN is often applicable by city network providers, as well as in enterprises. The advantage of this method of implementation is the security of the communication channel, since it is possible to configure different levels of security. This is ensured by setting up one network over another and accessing the Internet through two different networks.
- Inside the corporate network. Integration into one network allows secure access to the network by any number of employees' computers, regardless of their location and distance from the server.
- Combining components of the corporate network. Using VPN to ensure the interaction of various parts of the enterprise, it is possible to arrange access for them to individual resources of the common network.
The implementation of the technology is available for various devices, the operating system of which supports the option or there is a VPN client capable of forwarding ports using TCP / IP to a virtual network. The user can independently perform all the steps to configure. The need for this arises not even for the purpose of circumventing regional locks, because for this you can not configure VPN in your computer (to visit blocked resources, it is enough to install a third-party application, install a special browser extension, or use the browser’s built-in functionality). Configuring VPN on a PC or laptop is often required in case of changing the provider to set up Internet access. Setting up a VPN for Linux has its own specific features, given the versatility of the OS, but the principle remains the same.
Setup of server part on Linux
Consider creating a PPTP VPN server on the Ubuntu Server platform. With Linux, it is easy enough to deploy a server and this can be done even on a weak device. It is easiest to implement VPN with PPTP, since the implementation does not require the installation of certificates on client devices, and authentication is performed by entering a name and password. First you need to install the packages:
sudo apt-get install pptpd
When packages for PPTP VPN are installed, the server should be configured. To set the address range and perform other general settings, open the file /etc/pptpd.conf (edited with administrator rights):
nano /etc/pptpd.conf
To distribute more than a hundred connections at once, find Connections. This parameter should be uncommented, after which we indicate in this line the necessary value for the number of connections. To send broadcasting packets over VPN, you will have to uncomment the bcrelay parameter. Next, go to the end of the file, where we set up the addresses. Add the server address to the VPN network:
localip 10.0.0.1
The range of addresses to distribute to clients (we allocate immediately with some margin, since increasing the number without restarting pptpd will not work):
remoteip 10.0.0.20-200
If you have several external IPs, you can specify on which of them to listen to the PPTP incoming interfaces:
listen external ip
The speed parameter allows you to set the connection speed (bps). Save and close the file. The remaining parameters can be configured in / etc / ppp / pptpd-options:
sudo nano / etc / ppp / pptpd-options
In the #Encryption sector, which is responsible for encryption, strings that prohibit the use of outdated and insecure authentication methods should be uncommented:
refuse-pap
refuse-chap
refuse-mschap
The proxyarp option must be enabled, it is responsible for enabling proxy ARP server support. The lock option allows you to allow (for this comment) or prohibit (for this uncomment) the user multiple connections. Save and close the file. Server configuration is complete, but to create clients, we make the appropriate entries in / etc / ppp / chap-secrets:
sudo nano / etc / ppp / chap-secrets
They look something like this:
username1 * password12345 *
username2 10.10.12.11 password345 *
username3 * password787 10.10.11.21
For each user, write his name, password, remote and local IP, separating the information with the space bar. We prescribe a remote address if the client has a static IP and if it is used exclusively, otherwise it is preferable to put an asterisk so that the connection is uniquely made. The local address is specified when the user is allocated the same IP on the VPN network. In the example above, for the client in the first variant, connections are made from any external IP, the local one is allocated the first available. In the second case, the local one will be allocated the first available one, but connections are made only from the specified address. In the third - you can connect to the network from any address, while the local one will be allocated the one that was registered by us. The configuration of the VPN PPTP server is complete, restart it:
sudo service pptpd restart
The device itself does not need to reboot.
Configure VPN Clients
You can set up the client side of the VPN server in any OS, but we will configure it on Ubunt. By and large, the connection will work with the parameters set by default, but it is better to specify the type of connection and perform some other settings. Installing VPN on Ubuntu involves the following steps:
- In the "System" menu, go to "Settings" and select "Network Connections".
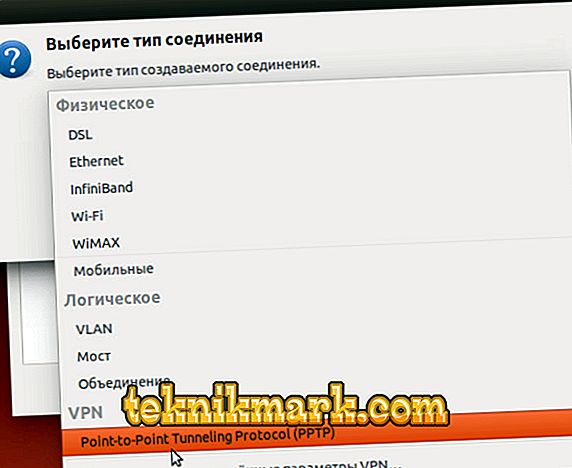
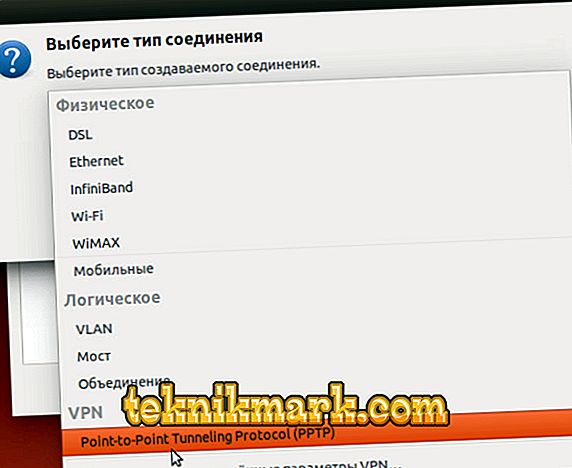
- Select the point-to-point PPTP tunneling connection type.
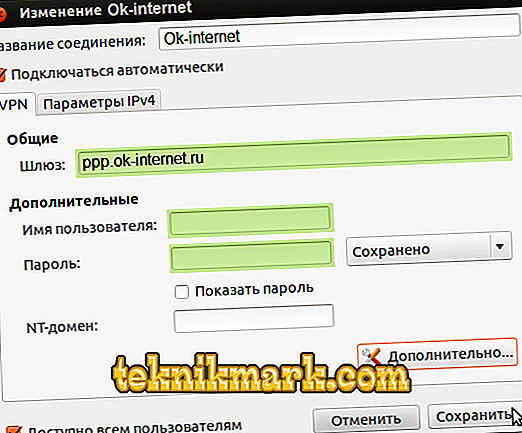
- We assign a name to the connection or leave it as provided.
- In the “Gateway” field we drive in the external IP of the server, enter the name and password (on the right side of the password field there is an option to save it for this user).
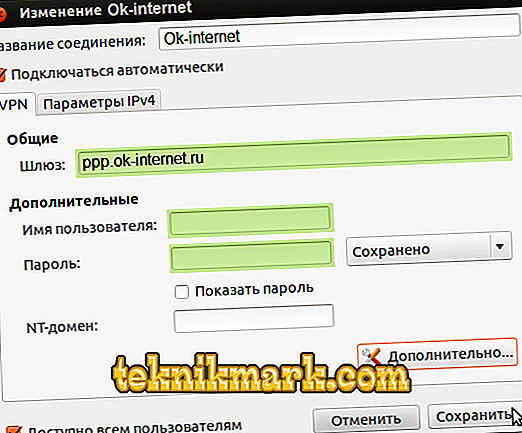
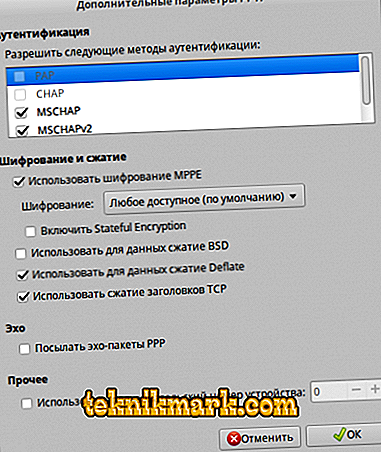
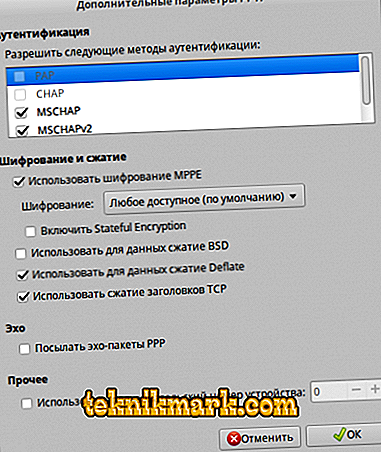
- Click "Advanced" and in the new window check the box next to "Use MPPE encryption" (this is a prerequisite for communicating with the server).
- Now we close the windows and connect to our server.
Configuring the VPN for Linux is complete, and devices can be connected locally, but to log in to the Internet through VPN, some more configuration will be required.
Setting up Internet access via VPN
When we have dealt with the local network, we begin to configure the Internet connection. To make a connection in the terminal, we write the following commands:
iptables -t nat -A POSTROUTING -o eth0 -s 10.0.0.1/24 -j MASQUERADE
iptables -A FORWARD -s 10.0.0.1/24 -j ACCEPT
iptables -A FORWARD -d 10.0.0.1/24 -j ACCEPT
By 10.0.0.1/24 is meant the local server IP and network mask. We remain:
iptables-save
and confirm the new parameters:
iptables-apply
Now on Linux there is the ability to connect to the Internet via VPN, as well as the other advantages of working with a virtual network. Visited resources will see the external address of the server, which will determine privacy, and the connection will be reliably protected from hacker attacks and ensure the security of data transmission.